Linux File Permissions and ACLs: Understanding Access Control
In the world of Linux system administration, two silent sentinels stand guard: file permissions and Access Control Lists (ACLs). They define who can access and manipulate your data. In this guide, we'll unravel their secrets, giving you the keys to master file security on your Linux system. Whether you're safeguarding your server or managing a shared workspace, understanding these guardians of data is crucial for maintaining both privacy and accessibility.
File Permissions:
In Linux, file permissions are represented by three sets of permission bits associated with different categories of users:
Owner (User): The user who owns the file or directory.
Group: The group that owns the file or directory.
Others: All users with access to the system who are neither the owner nor part of the group.
Each set of permissions consists of three bits, which can be:
r(read): Grants the ability to read a file or list the contents of a directory.w(write): Permits modifications to the file or directory, including creating, deleting, or renaming files within a directory.x(execute): Allows the execution of a file as a program or grants access to the contents of a directory.
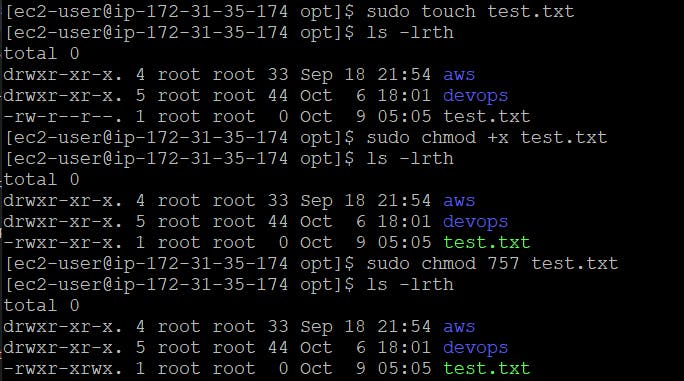
Managing file permissions involves using commands such as ls, chmod, chown, and chgrp. For instance, you can use the chmod command to alter permissions on a file:
chmod +x filename # Adds execute permission chmod -w filename # Removes write permission
If you want to change its ownership of a file to a different user, such as "testuser." You can use the chown command as follows:
sudo chown testuser example.txt
Let's say you have a directory named "project" that currently belongs to the "developers" group, but you want to change its group ownership to "designers." You can use the chgrp command like this:
sudo chgrp designers project
You can assign file permissions using numbers by using a numeric notation known as octal notation. In this notation, each permission is represented by a three-digit number, where each digit corresponds to a category of users: owner, group, and others. Within each digit, individual permissions are represented by values:
4represents read permission (r).2represents write permission (w).1represents execute permission (x).0represents no permission.
For example:
To set read and write permissions (rw) for the owner and group but no permissions for others, you can use the octal number 660 (4 for read + 2 for write for the owner and the group, and 0 for others).
chmod 660 filename
Note: Remember that when using octal notation, you're setting permissions for all three categories (owner, group, and others) simultaneously. Be cautious when using this method, as it can easily result in unintended permissions if not calculated carefully.
Here are some demonstrations:
Access Control Lists (ACLs):
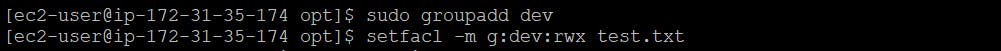
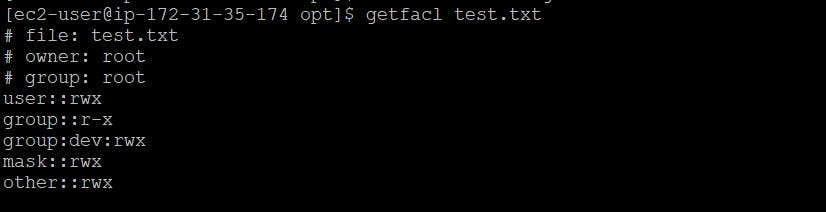
Access Control Lists (ACLs) provide more fine-grained control over file and directory permissions compared to the traditional Unix permissions system. ACLs allow you to specify access rights for specific users and groups beyond the owner, group, and others.
With ACLs, you can grant or deny permissions to individual users and groups, making it easier to manage complex access control scenarios. ACLs are particularly useful in multi-user environments and when more detailed access control is required.
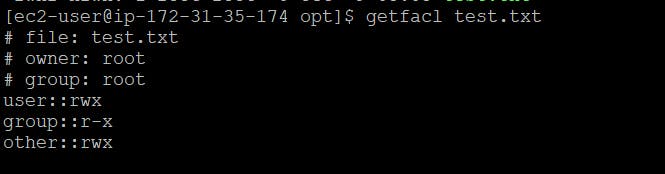
To work with ACLs in Linux, you can use commands like getfacl and setfacl. Here's a basic example of setting an ACL to grant read and write access to a specific user on a file:
setfacl -m u:username:rw filename
In this command:
-mspecifies that you're modifying the ACL.u:username:rwgrants read and write permissions to the user with the username "username."
To remove a specific ACL entry, you can use the --remove option. For example, to remove the ACL entry for "user2" on a file, you can use:
setfacl --remove u:user2 filename
To view the ACLs of a file or directory, you can use the getfacl command. For example:
getfacl filename
Here are some demonstrations:
To grant read and write permissions to a specific group (e.g., "dev") on a file (e.g., "test.txt"), you can use the following command:
Summary
Both file permissions and ACLs work together to control access to files and directories in Linux, allowing administrators to enforce security policies and manage user access effectively. The choice of which mechanism to use depends on the complexity of your access control requirements and your specific use case.
Thank you!